By opening ports from the Internet to your raspberry pi (ssh, http, ftp, https etc.), …
How to
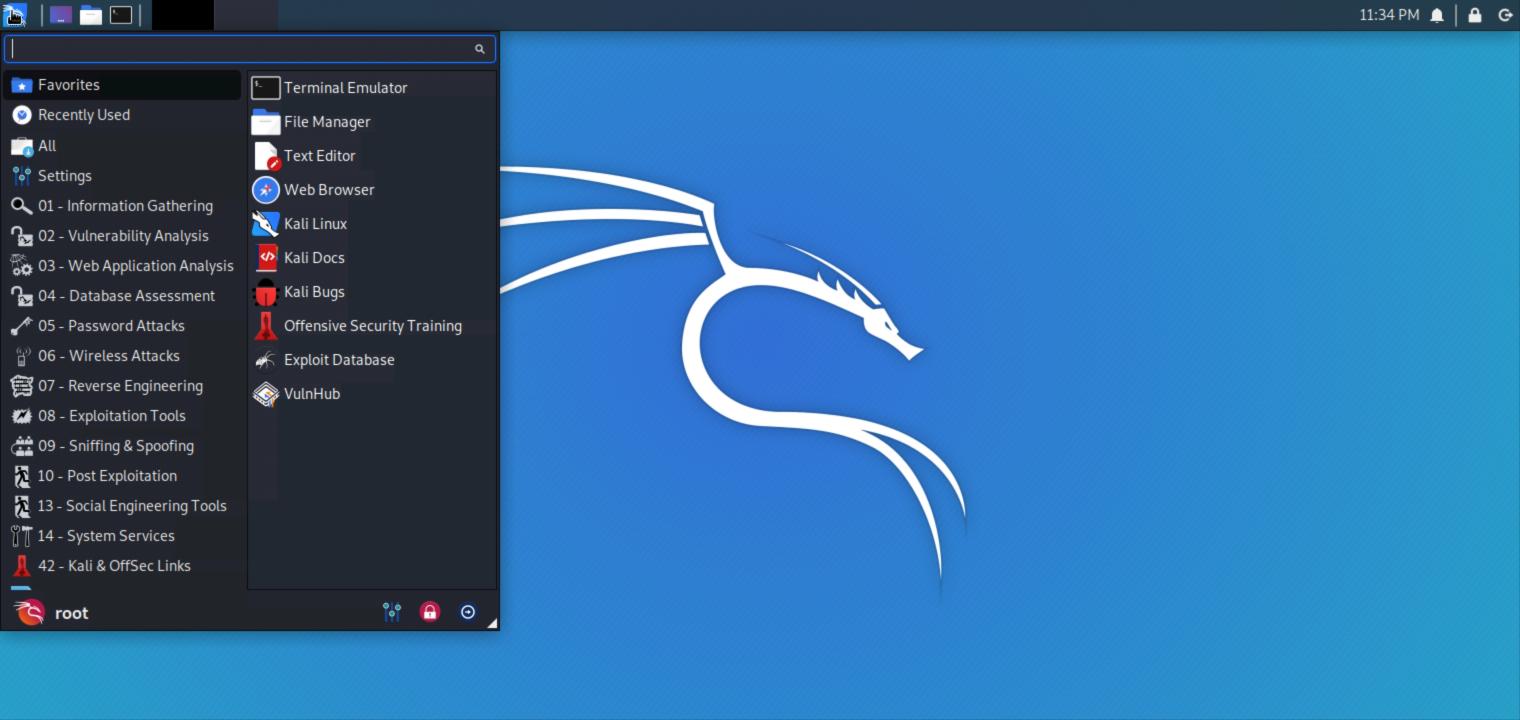
In this tutorial series called Hacking for beginners, we are going to teach you how …
The common mindset when it comes to considering a website’s success is that owners need …
When you are working in a hybrid environment where both on-premises Exchange Server and Office …
Netflix is one of the best resources for entertaining content today, as it offers a …
Have you ever wondered who viewed your Facebook profile? I know you have done it …
There are many commands that can irreversibly damage your system. Some are less cryptic than …
Sometimes you need to find out what is average response time of your website. Such …
You’ve just issued time-consuming command in UNIX/LINUX. Suddenly you need to leave or turn off …
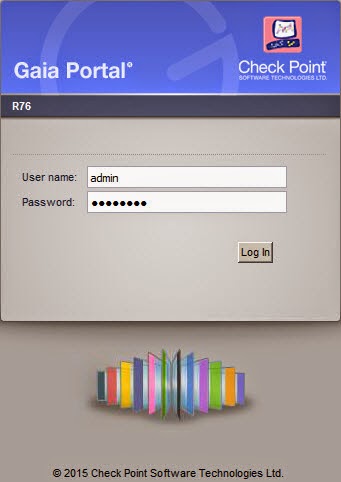
Sometimes you need to reset your admin or expert password in GAIA and you do …