WannaCry ransomware – hitting world right now uses NSA windows exploit
Earlier today, a massive ransomware campaign hit computer systems of hundreds of private companies and public organizations across the globe – which is believed to be the most massive ransomware delivery campaign to date. The Ransomware in question has been identified as a variant of ransomware known as WannaCry ransomware (also known as ‘Wana Decrypt0r,’ ‘WannaCryptor‘ or ‘WCRY‘).
Like other nasty ransomware variants, WannaCry also blocks access to a computer or its files and demands money to unlock it. Once infected with the WannaCry ransomware, victims are asked to pay up to $300 in order to remove the infection from their PCs; otherwise, their PCs render unusable, and their files remain locked.
In separate news, researchers have also discovered a massive malicious email campaign that’s spreading the Jaff ransomware at the rate of 5 million emails per hour and hitting computers across the globe.
| ALSO READ: WannaCry ransomware: researcher halts its spread by registering domain for $10.69
Ransomware Using NSA’s Exploit to Spread Rapidly
What’s interesting about this ransomware is that WannaCry attackers are leveraging a Windows exploit harvested from the NSA called EternalBlue, which was dumped by the Shadow Brokers hacking group over a month ago.
Microsoft released a patch for the vulnerability in March (MS17-010), but many users and organizations who did not patch their systems are open to attacks. The exploit has the capability to penetrate into machines running unpatched version of Windows XP through 2008 R2 by exploiting flaws in Microsoft Windows SMB Server. This is why WannaCry campaign is spreading at an astonishing pace.
Once a single computer in your organization is hit by the WannaCry ransomware, the worm looks for other vulnerable computers and infects them as well.
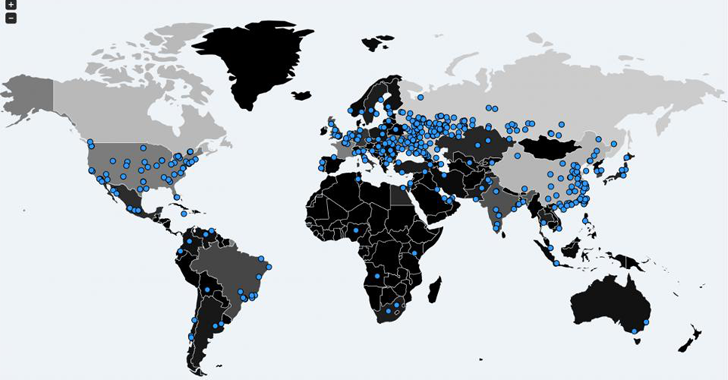
Infections from All Around the World
According to a report, the ransomware attack has shut down work at 16 hospitals across the UK after doctors got blocked from accessing patient files. Another report says, 85% of computers at the Spanish telecom firm, Telefonica, has get infected with this malware.
Another independent security researcher, MalwareTech, reported that a large number of U.S. organizations (at least 1,600) have been hit by WannaCry, compared to 11,200 in Russia and 6,500 in China.
Screenshots of the WannaCry ransomware with different languages, including English, Spanish, Italian, were also shared online by various users and experts on Twitter. Bitcoin wallets seemingly associated with WannaCry were reportedly started filling up with cash.
The Spanish computer emergency response organization (CCN-CERT) has even issued an alert that warns users of the “massive attack of ransomware” from WannaCry, saying (translated version):
“The ransomware, a version of WannaCry, infects the machine by encrypting all its files and, using a remote command execution vulnerability through SMB, is distributed to other Windows machines on the same network.”
It is unclear how the WannaCry ransomware is infecting systems, but obvious attack vector can be phishing emails or victims visiting a website containing malware.
“Power firm Iberdrola and utility provider Gas Natural were also reported to have suffered from the outbreak.,” according to BBC.
How to Protect Yourself from WannaCry
First of all, if you haven’t patched your Windows machines and servers against EternalBlue exploit (MS17-010), do it right now.
To safeguard against such ransomware infection, you should always be suspicious of uninvited documents sent an email and should never click on links inside those documents unless verifying the source.
To always have a tight grip on all your important files and documents, keep a good backup routine in place that makes their copies to an external storage device that is not always connected to your PC.
Moreover, make sure that you run an active anti-virus security suite of tools on your system, and most importantly, always browse the Internet safely.
source: http://thehackernews.com