Over 85% Of Smart TVs Can Be Hacked Remotely Using Broadcasting Signals
The Internet-connected devices are growing at an exponential rate, and so are threats to them. Due to the insecure implementation, a majority of Internet-connected embedded devices, including Smart TVs, Refrigerators, Microwaves, Security Cameras, and printers, are routinely being hacked and used as weapons in cyber attacks.
We have seen IoT botnets like Mirai – possibly the biggest IoT-based malware threat that emerged late last year and caused vast internet outage by launching massive DDoS attacks against DynDNS provider – which proves how easy it is to hack these connected devices. Now, a security researcher is warning of another IoT threat involving Smart TVs that could allow hackers to take complete control of a wide range of Smart TVs at once without having any physical access to any of them.
| ALSO READ: Vault 7: Top 15 Discoveries & Implications
Researcher Shows Live Hacking Demonstration
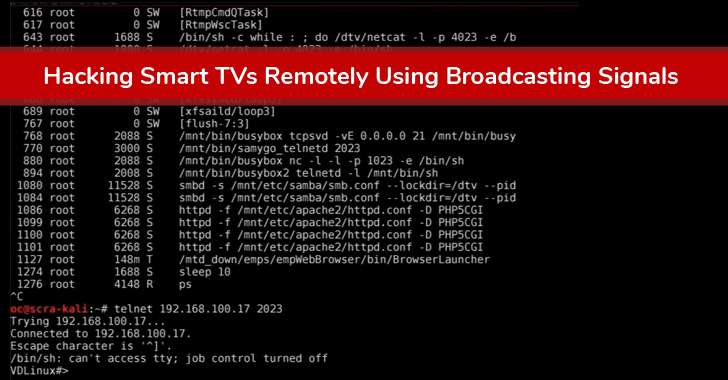
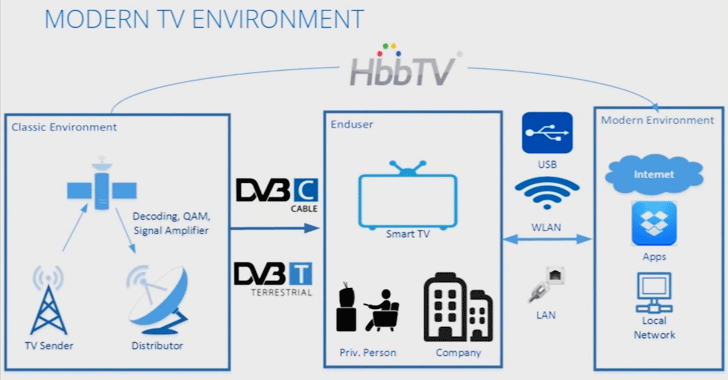
The proof-of-concept exploit for the attack, developed by Rafael Scheel of cyber security firm Oneconsult, uses a low-cost transmitter for embedding malicious commands into a rogue DVB-T (Digital Video Broadcasting — Terrestrial) signals. Those rogue signals are then broadcast to nearby devices, allowing attackers to gain root access on the Smart TVs, and using those devices for nasty actions, such as launching DDoS attacks and spying on end users.
Scheel provided a live hacking demonstration of the attack during a presentation at the European Broadcasting Union (EBU) Media Cyber Security Seminar, saying about 90 percent of the Smart TVs sold in the last years are potential victims of similar attacks. Scheel’s exploit relies on a transmitter based on DVB-T — a transmission standard that’s built into TVs that are connected to the Internet. The attack exploits two known privilege escalation vulnerabilities in the web browsers running in the background and once compromised, attackers could remotely connect to the TV over the Internet using interfaces, allowing them to take complete control of the device. Once compromised, the TV would be infected in a way that neither device reboots nor factory resets would help the victims get rid of the infection.
Scheel’s exploit is unique and much more dangerous than any smart TV hack we have seen so far. Previous Smart TV hacks, including Weeping Angel (described in the CIA leaked documents), required physical access to the targeted device or relied on social engineering, which exposes hackers to the risk of being caught as well as limits the number of devices that can be hacked.
However, Scheel’s exploit eliminates the need for hackers to gain physical control of the device and can work against a vast majority of TV sets at once. The hack once again underlines the risks of “Internet of Things” devices. Since the IoT devices are rapidly growing and changing the way we use technology, it drastically expands the attack surface, and when viewed from the vantage point of information security, IoT can be frightening.
source: http://thehackernews.com