Security Researcher Mathy Vanhoef of Imec-DistiNet discovered a weakness within the WPA2 protocol, potentially affecting …
News
Cryptocurrency trading can be a lucrative career and has already made many a person very, …
The HBO hackers who have been notoriously leaking unaired TV show episodes and their scripts …
Last year the Internet was taken down by cyber criminals through a massive Distributed Denial …
Earlier today, a massive ransomware campaign hit computer systems of hundreds of private companies and …
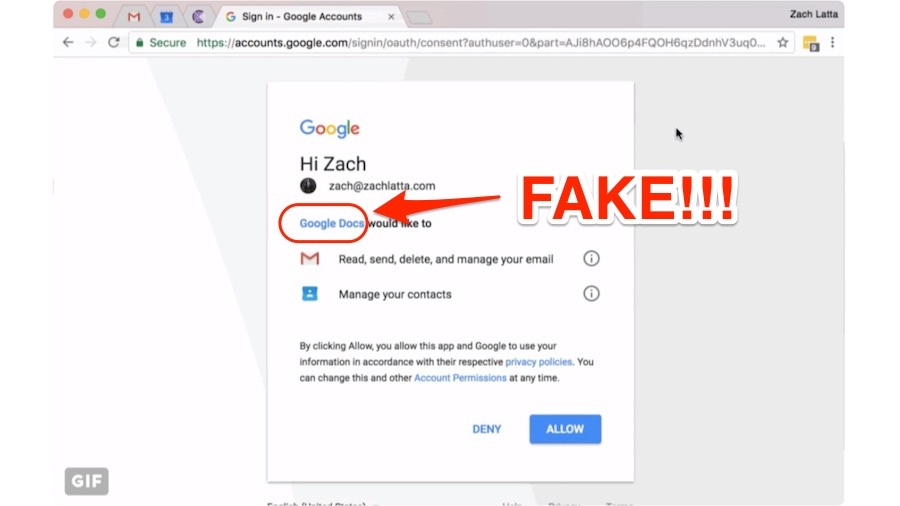
There are chances that you might’ve received an email with a Google document. It could …
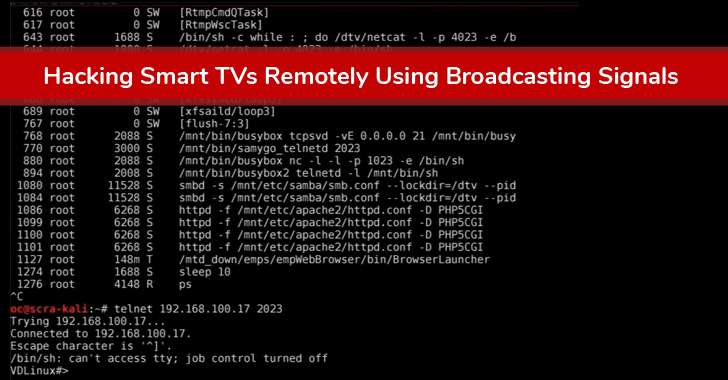
The Internet-connected devices are growing at an exponential rate, and so are threats to them. …
A team of researchers at Kaspersky Labs have recently cracked the mystery of a fileless …
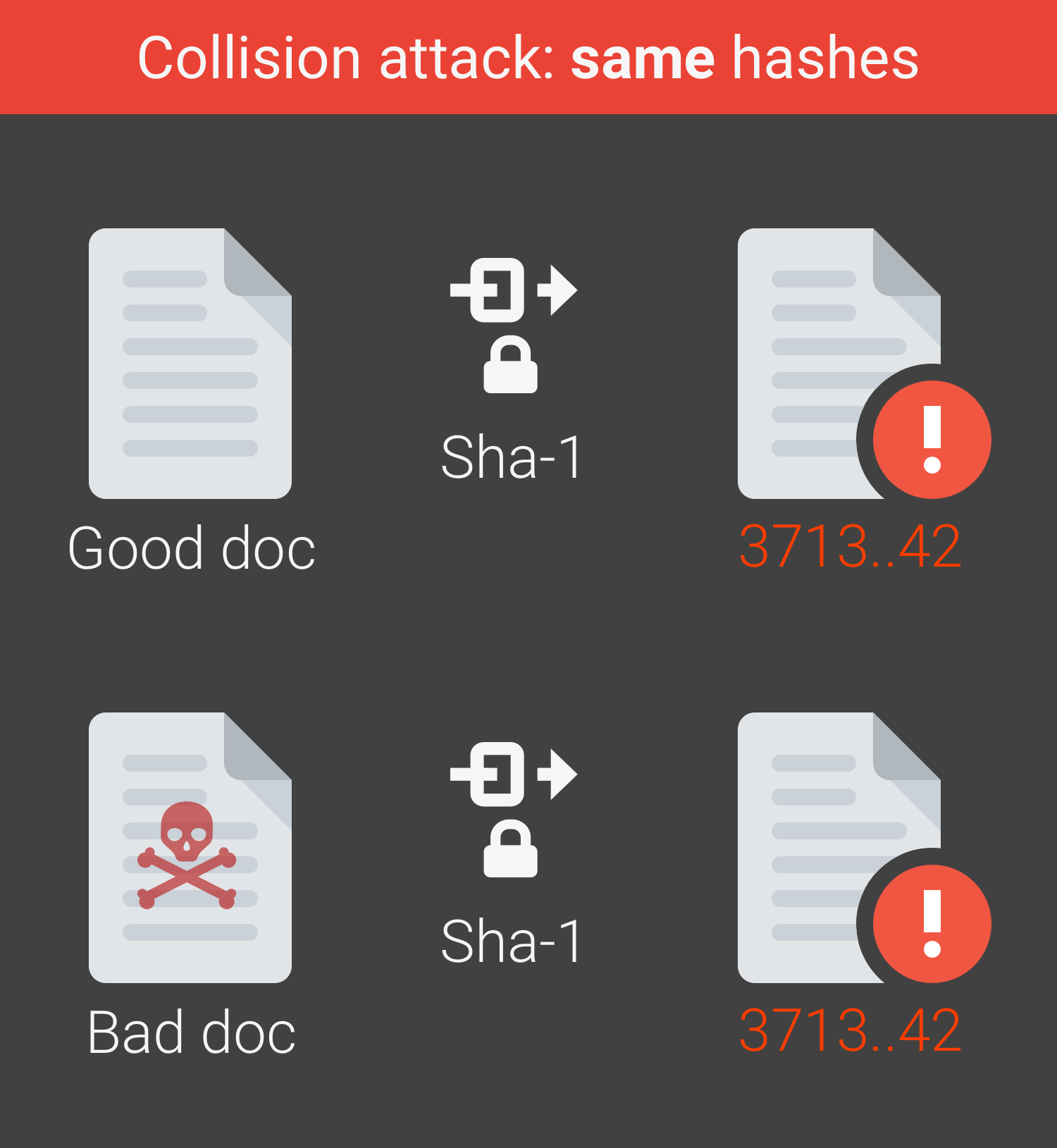
Researchers at Google have realized the first real world collision attack against SHA-1, creating two …
As we have already announced, WikiLeaks published CIA’s hacking capabilities, so called Vault 7. Hereby …