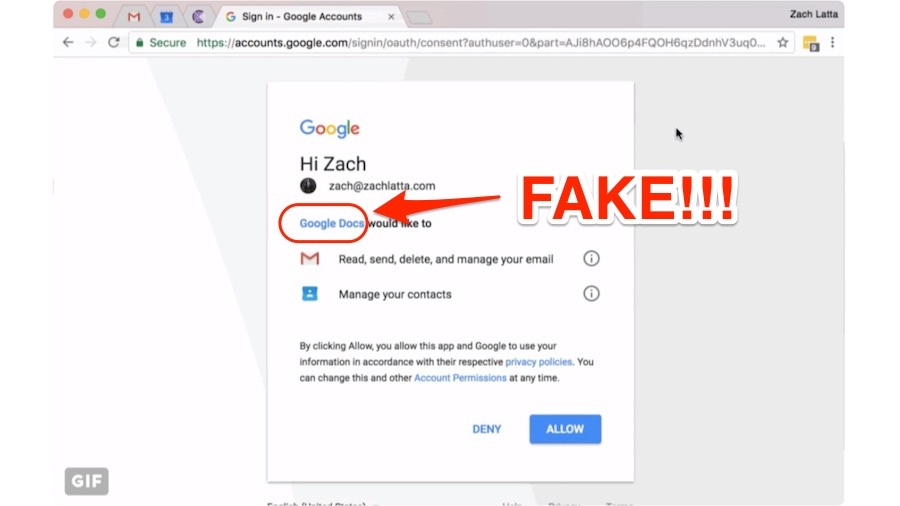
There are chances that you might’ve received an email with a Google document. It could be a phishing attempt that has gone viral. This attack has affected about 1 million Gmail users. While Google has blocked the attack, make sure to take security check and look for suspicious app permissions.
2017
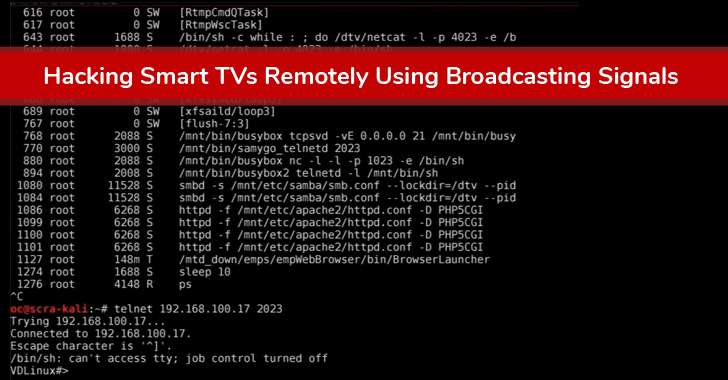
The Internet-connected devices are growing at an exponential rate, and so are threats to them. Due to the insecure implementation, a majority of Internet-connected embedded devices, including Smart TVs, Refrigerators, Microwaves, Security Cameras, and printers, are routinely being hacked and used as weapons in cyber attacks.
A team of researchers at Kaspersky Labs have recently cracked the mystery of a fileless malware that was used to hack bank ATMs in Russia and steal $800,000 in a single night. It was possible because of the two log files unintentionally left on the machine by the attackers. The researchers were able to reverse engineer the attack.
Analytics supports regular expressions so you can create more flexible definitions for things like view filters, goals, segments, audiences, content groups, and channel groupings. In the context of Analytics, regular expressions are specific sequences of characters that broadly or narrowly match patterns in your Analytics data.
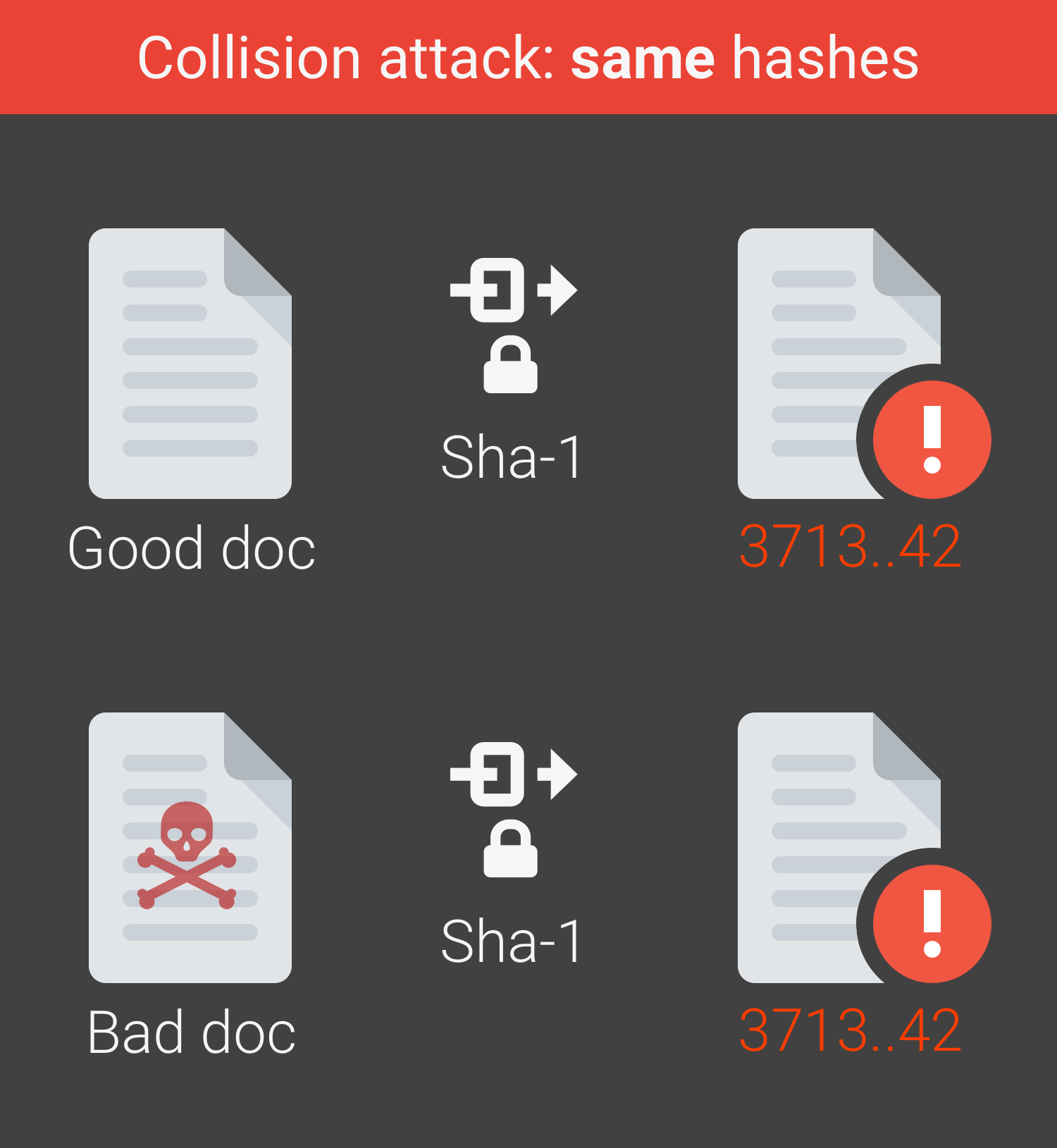
Researchers at Google have realized the first real world collision attack against SHA-1, creating two documents with different content but identical hashes.
Hacker Reveals Easiest Way to Hijack Privileged Windows User Session Without Password
Alexander Korznikov, an Israeli security researcher, has recently demonstrated that a local privileged user can even hijack the session of any logged-in Windows user who has higher privileges without knowing that user’s password, using built-in command line tools.
No one would argue the fact that Google is one of the most useful sites on the Internet. Unfortunately, most people only use about 3% of its power. Let’s play with google and find out hidden features.
Everybody knows how to use search engine “google”. But do you know tips, tricks and operators which can be used for google hacking? Here’s a tutorial that will teach you how to use google to hack and obtain even more specific data. Enjoy!
As we have already announced, WikiLeaks published CIA’s hacking capabilities, so called Vault 7. Hereby we are providing list of top 15 discoveries & implications.
On 07/03/2017, Wikileaks published a massive collection of data which is the biggest ever leak on CIA (Central Intelligence Agency). This immediate sensational news highlights the hacking capabilities for of CIA.